German Bundeswehr starts own Responsible Disclosure Program (VDPBw)
Bundeswehr Responsible Disclosure Program (VDPBw)
Today, on october 22, the German Armed Forces "Bundeswehr" officially launched the new Responsible Disclosure Program for reporting vulnerabilities and security vulnerabilities. Preparations have been underway for a few weeks now and can be clearly seen on the domain in the updates of the provided "Security.txt". Some of the links behind it do not work yet, because the program will be officially released today with an announcement of the German Armed Forces. An update of the current status can be seen on the twitter page of Kommando CIR of the Bundeswehr.
In recent years, we have also repeatedly reported security gaps and vulnerabilities in the digital environment to the Bundeswehr. Through permanent reports from security researchers, it may have become clear to the Bundeswehr that exponential added value could be created here in the long term. Thus, the program was planned by the Bundeswehr, rules were drafted, contents of the program were legally reviewed and administrative measures were issued.
Since the German Armed Forces never had a reporting office for security breaches with a Responsible Disclosure Program, there was mistrust in the project and skepticism in the handling of some high-ranking decision-makers accordingly. Probably always with the question in mind: can damage be done, is there really any added value and what does it cost?
As is well known, public authorities find it difficult to introduce new things. In the end, the focus is on success for everyone. For the first time ever, a government agency dares to publish guidelines on how to submit security breaches. We hope that other Bundeswehr authorities will follow suit and recognize the added security value.
Explicite Rules
If you think that you can just start hacking, you will be disappointed very soon. The German Federal Armed Forces have drafted a clear set of rules that precedes similarly already known bug bounty or responsible disclosure programs. The active and legally binding rules are intended to protect researchers and the German Armed Forces when submitting security breaches.
The German Armed Forces do not guarantee any consequences by investigating authorities if the researcher does not exploit his reported vulnerability, there is no intelligence background and the vulnerability is kept secret from third parties until the actual patch date. In some special cases the same rules from the main website are visible for researchers in the different project pages of the german bundeswehr to ensure.
Scope
The program affects all digitally accessible systems of the German Armed Forces such as the German Armed Forces Hospitals (Berlin, Koblenz & Co.), the German Armed Forces Universities (Munich & Hamburg) and many more. Anyone searching for Bundeswehr institutions via Google will quickly find other interesting services and projects of the Bundeswehr. Whitehat hackers and security researchers therefore have all the time to test their personal skills on the domains after insight and compliance with the rules.
In the objective the following vulnerability types are given as examples that qualify for the program:
- Cross Site Request Forgery (CSRF)
- Cross Site Scripting (XSS)
- Insecure Direct Object Reference
- Remote Code Execution (RCE) – Injection Flaws
- Information Leakage an Improper Error Handling
- Unauthorized access to properties or accounts
Like in all public programs here are some security vulnerabilities that are not accepted by the program, which are listed with examples as follows:
- Attacks that require physical access to a user's device or network
- Forms with missing CSRF tokens (exception: criticality exceeds Common Vulnerability Scoring System (CVSS) level 5)
- Missing security headers that do not directly lead to an exploitable vulnerability
- The use of a library known to be vulnerable or publicly known to be broken (without active proof of exploitability)
- Reporting automated tools or scans without explanatory documentation
- Social engineering against persons or facilities of the German Armed Forces and their contractors
- Denial of Service attacks (DoS/DDoS)
- Bots, SPAM, mass registration
- No submission of best practices (e.g. certificate pinning, security header)
- Use of vulnerable and "weak" cipher suites / ciphers
Communication
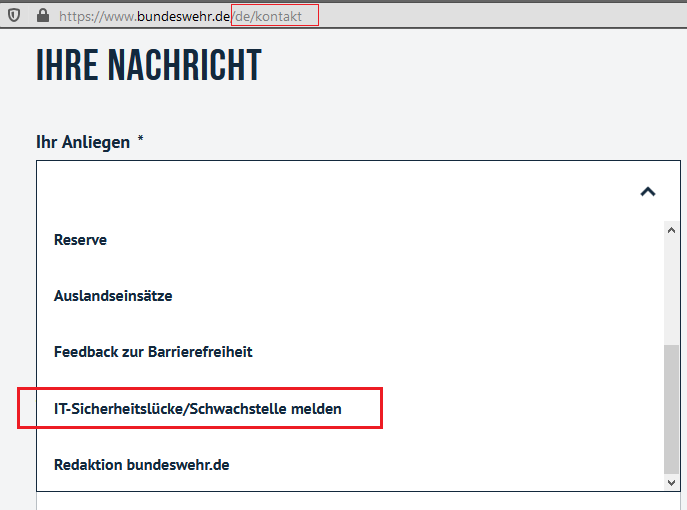
Entries of weak points must be made via email or contact form on the Bundeswehr website. Successful submissions will be rewarded with an entry in the Hall of Fame (Acknowledgements) on the official domain of the Bundeswehr. In addition, there is a possibility for security researchers who wish to remain anonymous to choose to remain anonymous permanently without appearing in public. The coordination and communication in the processing of reports is handled by the Center for Cyber Security, which has proven itself successfully on several occasions. There is a PGP key for secure communication when reporting a security breach.
Another good option for security researchers are the templates for submitting their own vulnerabilities. Security researchers can use the following template, which was provided by the German Federal Armed Forces.
1. Titel / Bezeichnung der Schwachstelle
2. Schwachstellentypus
3. Kurzerklärung der Schwachstelle (ohne technische Details)
4. Betroffenes Produkt / Dienst / IT-System / Gerät
a. Hersteller
b. Produkt
c. Version / Modell
5. Exploitationtechnik
a. Remote
b. Local
c. Netzwerk
d. Physisch
6. Authentication-Typ
a. Pre-Auth
b. Authentification Guest
c. Benutzer-Privilegien (User / Moderator / Manager / Admin)
7. Benutzerinteraktion
a. Kein Benutzer
b. Niedrige Benutzerinteraktion
c. Mittlere Benutzerinteraktion
d. Hohe Benutzerinteraktion
8. Technische Details und Beschreibung der Schwachstelle
9. Proof of Concept
10. Aufzeigen einer Lösungsmöglichkeit
11. Autor und Kontaktdaten
12. Einverständnis zur Nennung des Namens und der gefundenen Schwachstelle in der Danksagung
The concepts follow public examples like Hack the Pentagon or Hack the Air Force Responsible Disclosure programs of the US military. whether the responsible disclosure program will end up as a bug bounty program with commercial prizes depends solely on the researchers and coordinators of the Bundeswehr. We would like to thank the German Federal Armed Forces for providing a set of rules and regulations to give the whitehat community legal security and for sending in any weaknesses found.
We hereby call upon all german and international security researchers and whitehat hackers (Fr13nd5) out there to actively participate in the official Responsible Disclosure Program of the German Armed Forces "Bundeswehr" in accordance with the existing set of rules. If you have any questions about the topic or program, please contact the Bundeswehr press office directly or send us an email.
Note: Please do not submit any bugs or security vulnerabilities in the German Armed Forces by external researchers to our Vulnerability Lab Research Team. If you have any questions regarding identified vulnerabilities or weaknesses, please contact directly security@bundeswehr.org.
References:
https://www.bundeswehr.de/de/security-policy/danksagung
https://www.bundeswehr.de/security.txt
https://www.bundeswehr.de/de/security-policy
Public Press:
https://www.presseportal.de/pm/129406/4741260
https://background.tagesspiegel.de/digitalisierung/bundeswehr-laedt-hack...
https://portswigger.net/daily-swig/german-armed-forces-launch-security-v...
https://netzpolitik.org/2018/schwachstellen-management-wie-deutsche-beho...



Comments
i want to participate in the
freue mich, dass die
Well done *smile
läuft sehr geile aktion,
Add new comment