Rhein Ruhr Express (RRX) - DNS Cache Snooping Vulnerability on Wifi Hotspot

DNS Cache Snooping Vulnerability on Wifi Hotspots by Siemens
The Rhein-Ruhr-Express (RRX) is a program currently being implemented to provide regional transport on the core route of the Ruhr area and the central Rhineland from Dortmund via Essen, Duisburg and Düsseldorf to Cologne. The
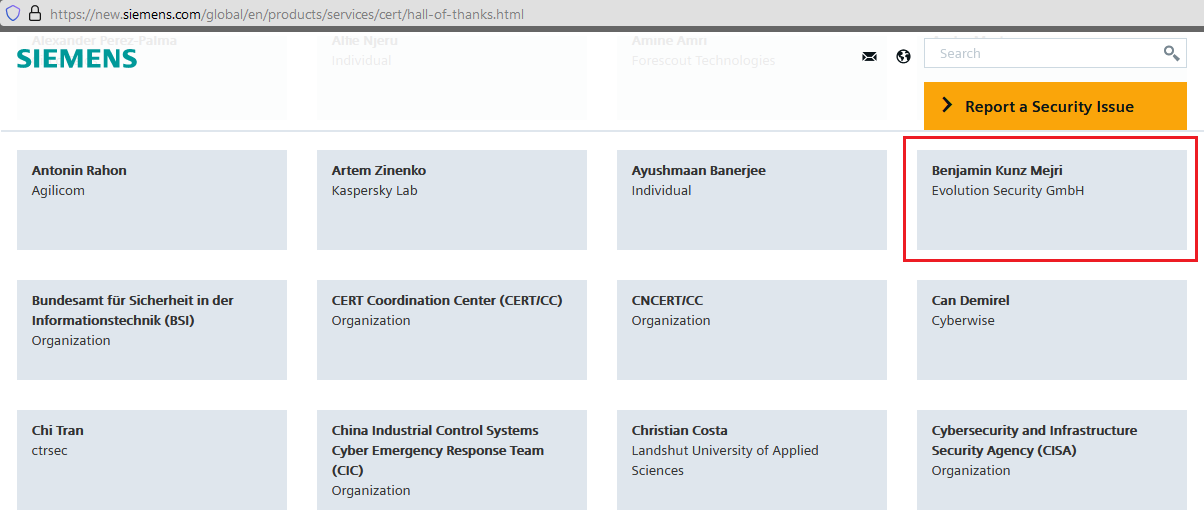
Due to a short trip by one of our top core team researchers "Benjamin Kunz Mejri" 1 medium severity vulnerability in the Siemens Hotspot Hardware with the RRX IOB Landing Page v1.0 has been discovered. The technical details and information are serious and allows a remote attacker to spy and manipulated customers using the wifi hotspots in trains.
During his quick testing live in the rail he sent a non-recursive query for a test.com domain for example and finally received 1 answer via dnsmasq-2.75. Finally he figured out that the remote dns server responds to queries for third-party domains that do not have the recursion bit set.
Non-recursive query test.com
Received 1 answer: dnsmasq-2.75
92.184.213.27
53 / udp / dns
-
Hosts
53 / udp / dns
192.168.44.1
Using this information the researcher was finally able to determine which domains have recently been resolved via this name server, and therefore which hosts have been recently visited. In a further step he figured out that this may include employees, consultants and potentially users on the network. Means in plain-text that it is possible to see what services you are using and which domains you are requesting from outside. In a simple attack it allows a remote attacker via wifi to tamper other users that are processing to resolve a website (Exp. paypal.de, amazon.de, ebay.de & co.) via dns. A dns cache snooping attack could be possible even if the DNS server is not configured to recursively resolve for third parties, as long as it provides cache records also to third parties. When audited or exploited, a dns server implementation is vulnerable to cache snooping cyber attacks that allow a remote attacker to identify for example which domains or hosts have been recently resolved by a given name server.
After the issues were identified our team reported the vulnerability directly to the Rhein Ruhr Express contact. A short time later the siemens cert team started to contact us and we replied successfully.
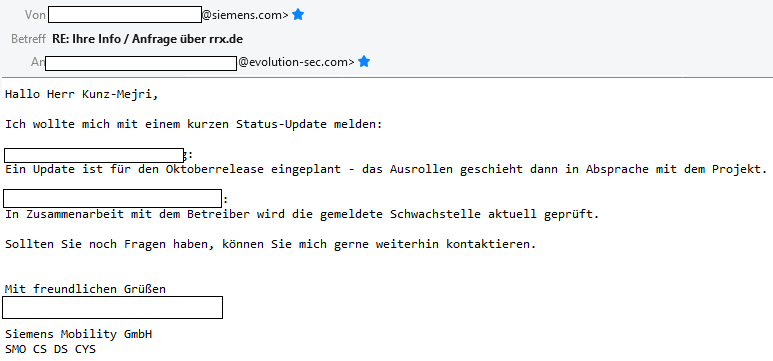
Short time later the vulnerability has been confirmed with medium severity and a patch will be available in mid of october 2020 that is deployed until 2022 to several train of the series. The patching process will be delivered by siemens during train maintenance and will take at least until 2022 Q2-Q3 to be rolled out on all trains (40+). Thanks to the siemens cert team that was directly in touch to resolve the vulnerabilities in our public. With this point we would like to mention to readers to for sure ever improve the security and not blindly trust a free wifi in your next train or rail on your trips around the world. However this issue has been successfully resolved by the manufacturer, thanks!
Acknowledgements:
Advisory:
https://www.vulnerability-lab.com/get_content.php?id=2261
Picture Source: © Kompetenzcenter Marketing NRW (KCM)



Add new comment