PayPal Inc Bug Bounty - JDWP Remote Code Execution Vulnerability
PayPal Inc Bug Bounty - JDWP Remote Code Execution Vulnerability
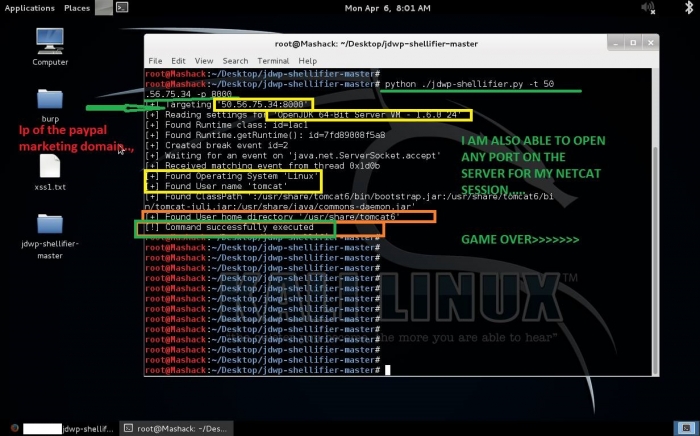
In the last weeks a new security researcher "Milan A Solanki" was activly reporting security bugs to paypal and ebay inc. One of his valid and verified issues was exclusivly disclosed by the vulnerability laboratory infrastructure. In april Milan A Solanki discovered a remote code execution vulnerability in the marketing online service web-application of paypal. The issue was marked as critical with a cvss count of 9.3.
The Java Debug Wire Protocol (JDWP) is the protocol used for communication between a debugger and the Java virtual machine (VM) which it debugs (hereafter called the target VM). JDWP is one layer within the Java Platform Debugger Architecture (JPDA). JDWP does not use any authentication and could be abused by an attacker to execute arbitrary code on the affected server.
The tool that he used to disclose was the well known io-active script jdwp-shellifier. He scanned the marketing site and had opened port 8000 (pre-auth) than he just executed after the accepted connection his own codes/commands and finally disclosed a remote code execution issue to the official paypal inc bug bounty program. Within one week the paypal security team verified the vulnerability and patch the bug within two weeks after disclosure.
Vulnerable Protocol(s):
[+] JDWP
Port(s):
[+] 8000
The security researcher recorded a security video to demonstrate the vulnerability by a live hack session. The video is also available in our fresh feed and demonstrates the security risk of the vulnerability.
Reference(s):
http://www.vulnerability-lab.com/get_content.php?id=1474
http://www.vulnerability-lab.com/get_content.php?id=1475



Add new comment