Microsoft starts .NET Core & ASP.NET Bug Bounty Program
Microsoft Corporation starts .NET Core & ASP.NET Bug Bounty Program
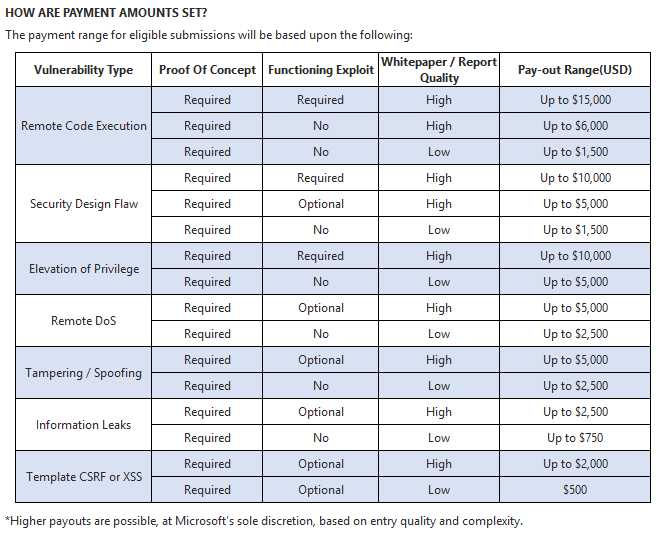
Today Microsoft Corporation expanded their Bug Bounty Program and it now covers also vulnerabilities in .NET Core CLR and ASP.NET 5. The program begins October 20, 2015, and ends on January 20, 2016. Microsoft published a new rewards list, higher payouts are possible, at Microsoft’s sole discretion, based on entry quality and complexity.
Qualified submissions are eligible for payment from a minimum of $500 USD to $15,000 USD, and bounties will be paid out at Microsoft’s discretion based on the quality and complexity of the vulnerability. Microsoft may pay more than $15,000 USD, depending on the entry quality and complexity. Our researcher team looks forward to participate in the new program. Microsoft won last year the "Best Upcoming Bug Bounty Program 2014" award.
Vulnerability submissions provided to Microsoft must meet the following criteria to be eligible for payment:
- Identify an original and previously unreported vulnerability in the latest beta or RC version of Microsoft CoreCLR, ASP.NET 5 and the default ASP.NET 5 templates provided with the ASP.NET Web Tools Extension for Visual Studio 2015. Examples may include bypasses of CSRF protection, Encoding, Data Protection failures, Information disclosures to a client, Authentication bypasses and Remote Code Execution.
- Include concise reproducibility steps that are easily understood. (This allows submissions to be processed as quickly as possible and supports the highest payment for the type of vulnerability being reported.)
Be sure to read all of these terms before sending Microsoft any submission: https://technet.microsoft.com/en-us/security/
Microsoft may reject any submission, that it determines (in its sole discretion) does not meet these criteria.
Reference(s):



Add new comment