Trend Micro DirectPass 1.5.0.x – Software Vulnerabilities
Trend Micro DirectPass 1.5.0.x – Software Vulnerabilities
The security researcher Benjamin Kunz Mejri from Vulnerability Lab have identified in march a security flaw in Trend Micro’s popular password manager cloud software “DirectPass”. DirectPass v1.5.0.1060 manages customer website and account passwords or login IDs in one secure location of Trend Micro's cloud network. The software provides Keystroke encryption, confidential notes, secure password generation and a secure browser engine module. The reported vulnerability affects the new password cloud software of Trend Micro.
The first vulnerability, catalogued as a “medium+ risk,” allows a local attacker to inject arbitrary commands from a low privilege system user account to compromise the software.
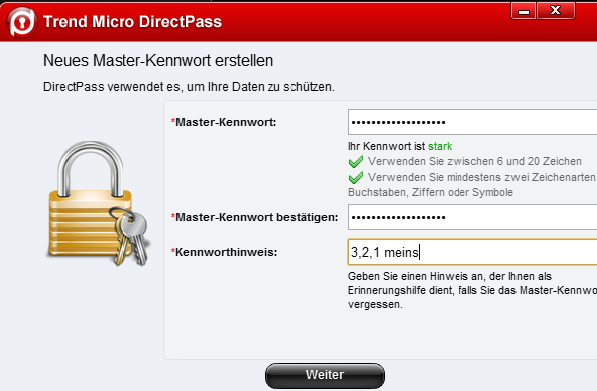
“The vulnerability is located in the DirectPass master password setup module of the Trend Micro InstallWorkspace.exe file. The master password module of the software allows users to review the included password in the secound step for security reason,” reads the advisory provided by Vulnerability Lab to Softpedia.

“The hidden protected master password will only be visible in the check module when the customer is processing to ‘mouse-over’ onto the censored password field. When the software is processing to display the hidden password in plain the command/path injection will be executed out of the not parsed master password context in the field listing.”
The second issue is a persistent input validation vulnerability that plagues the “directpass check” module and it can be triggered when “processing to list a manipulated master password.”

The vulnerability, which required medium user interaction, can be leveraged for persistent session hijacking, phishing, module context manipulation and persistent redirects to malicious websites.
The third and final bug is a critical pointer (DOS) vulnerability that can be exploited by a local attacker to crash the application or compromise the bound dynamic link library (libcef).

“Attackers can inject scripts with loops to mouse-over multiple times the hidden password check listing of the master password. The result is a stable crash down of the InstallWorkspace.exe. The problem occurs in the libcef.dll (1.1.0.1044) of the Trend Micro DirectPass v1.5.0.1060 software core,” the security expert explained.

All the vulnerabilities affect Trend Micro DirectPass 1.5.0.1600 software. The complete proof of concept and report of the security bugs is available here.
The laboratory also provides a demonstration video …
Trend Micro DirectPass v1.5.0.1060 (W7) - Multiple Software Vulnerabilities
VIDEO HERE > https://www.youtube.com/watch?v=Mbf0KqvSERs <
Trend Micro was cooperative and confirmed the zero day vulnerabilities in the software. The developer team is provids a full patch for all three security issues with one large patch. The patch is available on the trend micro update server service for customers.
Trend Micro Solution ID: 1096805
Time-Line: Responsible Vulnerability Disclosure
2013-03-08: Researcher Notification & Coordination (Benjamin Kunz Mejri)
2013-03-09: Vendor Notification (Trend Micro - Security Team)
2013-03-16: Vendor Response/Feedback (Trend Micro - Karen M.)
2013-05-09: Vendor Fix/Patch (Trend Micro - Update Server)
2013-05-21: Public Disclosure (Vulnerability Laboratory)
Trend Micro: (KB) - http://esupport.trendmicro.com/solution/en-US/1096805.aspx

We appreciate to work with trend micro and also need to say thanks to Karen M.! She coordinated the exchange of information regarding the issue between the Laboratory & Trend Micro. She has requested more details to stable patch all 3 issues within 90 days after the report arrived.
Article (ED - Softpedia): http://news.softpedia.com/news/Experts-Find-Multiple-Security-Flaws-in-Trend-Micro-s-DirectPass-1-5-0-356425.shtml



Comments
game over trend micro. good
Add new comment