Apple iOS 8.0 - 8.0.2 - Controls Re Auth Bypass Vulnerability
Apple iOS 8.0 - 8.0.2 - Controls Re Auth Bypass Vulnerability
Due to the last years we learned fast that glitches can result in a security problem for embed device systems. At the beginning of the year a german core team researcher revealed information on how to permanently evade the controls to bypass with an app the pass code. The researcher used a combination of glitches and design errors in the phone ui of iOS to successful exploit the local issue. The issue has a minor severity then for example the emergency call issue of 2013 because a physical device by account access is required. (cvss 5.2)
A local pass code (code lock) bypass and glitch has been discovered in the Apple iOS v8.0 (12A365) mobile device system. The vulnerability allows to bypass or evade via glitch the regular pass code restriction of the embed iOS device system.
The local bypass vulnerability is located in the favorite contact preview function that can be used for imessages or phone calls. Local attackers with physical access can glitch the display by usage of siri to bypass since the end of a call the device system access restriction.
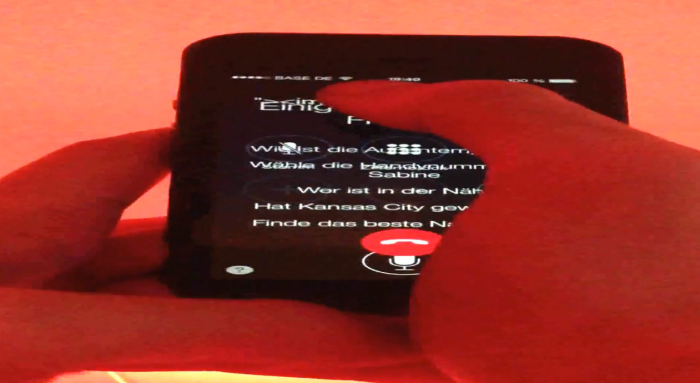
To exploit the attacker visit the favorite call function via the home button in the ios task favorite preview slideshow. He clicks a contact and uses siri to merge via glitch with the authorized call app. In the next step he locks the mobile device. The he hold the volume + button multiple times to keep the service since the call end ahead to the pass code logon screen. The issue is very tricky to exploit but affects at the end obviously secure pass code restriction. The attacker is able to multiple times push in the last moment the power button to deactivate the display and start the pass code lock. However the local attacker is able to bypass exactly this mechanism in the mentioned location.
During the tests the security researcher revealed a video that demonstrates the security issue and the glitch that affects the local device security. Like in the Samsung in 2010 the device allows to access the information as long as a call runs in the phone app. The local issue has been tested to verify with the default configured iphone 6 and 5s device.
The security risk of the local pass code bypass vulnerability is estimated as medium with a cvss (common vulnerability scoring system) count of 5.2. Exploitation of the local glitch bypass vulnerability requires a privileged web-application user account, multi user account or restricted physical device access without user interaction. Successful exploitation of the local pass code bypass vulnerability results in device compromise or information leaking.
Affected Device(s):
[+] Apple > iPhone 5 & 6
Affected OS Version(s):
[+] iOS v8.0 (12A365)
Tested Device(s):
[+] Apple iPhone 5s & 6 > iOS v8.0 (12A365)
Proof of Concept
The auth bypass vulnerability can be exploited by local attackers with physical device access without user interaction. For security demonstration or to reproduce the issue follow the provided information and steps below to continue.
Requirement(s):
[+] iOS v8.0 (default install)
[+] Apple Device (iPad 2, iPhone 5s or iPhone 6)
[+] Two healthy hands
Manual Steps to reproduce the local vulnerability ...
1. Start your iOS device and install the new iOS v8.0 to your ipad2, iphone 5s or iphone 6 device
2. Start the mobile and login to the pass code
3. Now press the home button twice to see the app preview slide show and the new favorite contract slideshow above
4. move you finger over the favorite contact and two symboles become visible (Phone app and Message app)
5. Press now the home button two seconds to activate siri and push in the last second the private call button to the contact
Note: Be fast! After it the siri which is in default mode available glitches ahead to the phone call
6. Now you push the power button on top of the mobile and shortly after it you use the hardware volumen to reactivate
Note: The mobile now goes in the locked mode after the power button push but the siri is ahead glitched to the call that runs
7. In the call mask you can click the contacts button by pressing around the button because of the siri glitch
8. The contact list becomes available as long as the call runs with the glitch through siri
9. Successul bypass of the secure pass code restriction!
After the issue was reported to apple the security researcher demonstrated the issue in a little tricky video. Regular the iOS phone ui jumps to the closed pass code back when processing to press the power button. Due to a misconfiguration the attacker is able to bypass the controls of the device to multiple times access the phone ui without the secure implemented pass code re-auth function.
Video: http://www.vulnerability-lab.com/get_content.php?id=1334
Advisory: http://www.vulnerability-lab.com/get_content.php?id=1322



Comments
iPhone 6s
hello....
Thank you very much for good information i will share this information on my social profile. This is good information about iPhone, I think all people like this very much.
Add new comment