BMW Mail - Persistent Validation Vulnerability
A vulnerability researcher of the vulnerability lab team disclosed a simple but effective technique that was used against microsoft and adobe some years ago. A persistent input validation web vulnerability has been discovered in the official BMW online service portal web-application.
The vulnerability is located in the `firstname` and `lastname` value parameters of the `mail` module. The vulnerable parameters are insecure sanitized next to being delivered inside of a basic html mail template.
Remote attackers are able to inject own malicious script code via POST method request to the application-side of the bmw domain mailing service. The attack vector of the vulnerability is persistent on the application-side and the request method to inject is POST. The attacker does not need to be directly authenticated because its only an initial registration without direct activiation request. The injection points are the vulnerable input fields in the BMW 4er Coupé registration formular and the execution of the malform injected code takes place in the `mail.bmw.de`, `m.mail.bmw.de` domains with the unique `/jsp/m.jsp` file by a client-side GET method request.
The issue affects all pages listed with the newsletter module. The vulnerability allows email spoofing, phishing, spamming, cross site requests for redirects to malware or exploits and persistent manipulation of bmw domain (email) contents. A targeted user can not see that the manipulated website is insecure because of the trusted native source that deliveres the contexts over the bmw mailing (mail.bmw.de).
The exploitation of the persistent input validation web vulnerability requires no or low user inter action and no privileged application user account. Successful exploitation of the vulnerability results in session hijacking, persistent phishing, persistent external redirects to malicious sources and persistent manipulation of affected web module context.
Request Method(s):
[+] POST
Vulnerable Module(s):
[+] BMW 4er Coupé - Registration Formular
Vulnerable Input(s):
[+] Vorname (Firstname)
[+] Nachname (Lastname)
Vulnerable Section(s):
[+] CONTENT
Vulnerablke File(s):
[+] m.jsp
Affected Domain(s):
[+] mail.bmw.de
[+] m.mail.bmw.de
The vulnerability can be exploited by remote attackers with low privileged application user account and medium required user interaction.
Payload: Phishing
Payload: Session Hijacking
Payload: Malware or Exploit
Payload: Redirect
View => https://www.vulnerability-lab.com/get_content.php?id=2262
PoC: Demo URLs (Examples Non Malicious!)
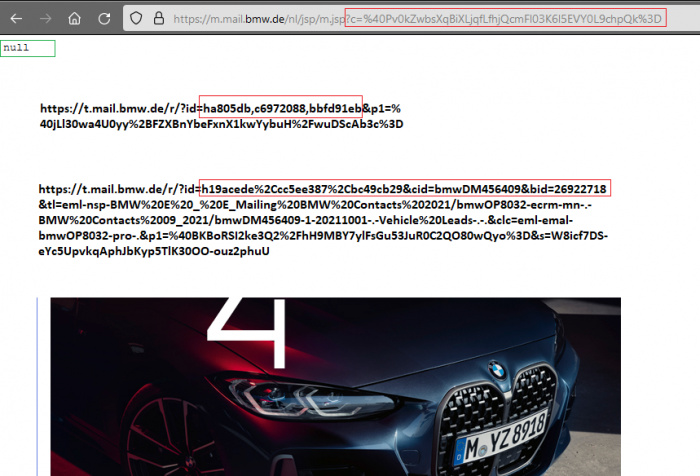
https://m.mail.bmw.de/nl/jsp/m.jsp?c=%40Pv0kZwbsXqBiXLjqfLfhjQcmFl03K6l5...
--- PoC Session Logs (GET) [Execute] ---
https://m.mail.bmw.de/nl/jsp/m.jsp?c=%40Pv0kZwbsXqBiXLjqfLfhjQcmFl03K6l5...
Host: m.mail.bmw.de
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:76.0) Gecko/20100101 Firefox/76.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,*/*;q=0.8
Accept-Language: de,en-US;q=0.7,en;q=0.3
Accept-Encoding: gzip, deflate, br
Connection: keep-alive
Cookie: uuid230=e171a7d5-3065-4691-9e39-dc051d6b6bb2; nlid=59b025|bd9a2846; bmwdtm_hq_userdata=lo:not logged in;
v_reco_data={"user":"returning","last_channel":"other","pages_viewed":{"https://www.bmw.de/de/index.html":2,
"https://configure.bmw.de/de_DE/configure/G22/11AP/FKFSW,P0668,S01S3":1},"site_sections_viewed":{"Index":2,"Configurator":1},
"session_duration":"622","configurator_session_duration":"8"}; at_check=true; bmwdtm_hq_vs=1591355369; s_lv=1591358075425; _cs_mk=0.8202769905305621_1591355369096;
_cs_c=1; _cs_id=d1d6f4a2-9e37-a0cf-fd19-495b95a51ace.1591355370.2.1591358075.1591358046.1.1625519370460.Lax.0;
AMCV_B52D1CFE5330949C0A490D45%40AdobeOrg=1585540135%7CMCMID%7C43471724831001338048363975029512836080%7CMCAID%7CNONE%7CMCOPTOUT-1591365306s%7CNONE%7CvVersion%7C4.4.0;
AMCVS_B52D1CFE5330949C0A490D45%40AdobeOrg=1;
s_ppvl=all-models%2520%253E%25204-series%2520%253E%2520coupe%2520%253E%25202020%2520%253E%2520bmw-4-series-coupe-highlights%2C93%2C65%2C6927%2C1920%2C884%2C1920%2C1080%2C1%2CP;
s_ppv=all-models%2520%253E%25204-series%2520%253E%2520coupe%2520%253E%25202020%2520%253E%2520bmw-4-series-coupe-models-equipment%2C100%2C100%2C7283%2C1920%2C884%2C1920%2C1080%2C1%2CP;
s_cc=true; dtTransferCookie==3=srv=2=sn=V9BCJG98FF13N2R0E8BB33TB9RSRD9AS=app:d6bac8ba1bbb22f2=1=ol=0=perc=100000=mul=1;
check=true; s_fid=%20;
last_config=%7B%22modelrange%22%3A%22G22%22%2C%22modelcode%22%3A%2211AP%22%2C%22ag_modelcode%22%3A%2211AP%22%2C%22brand%22%3A%22bmwCar%22%2C%22pain
t%22%3A%22P0668%22%2C%22rim%22%3A%22S01S3%22%2C%22fabric%22%3A%22FKFSW%22%2C%22options%22%3A%22FKFSW%2CP0668%2CS01CB%2CS01DF%2CS01S3%2CS0205%2CS0230
%2CS0255%2CS02PA%2CS02VB%2CS0428%2CS0431%2CS0493%2CS04AT%2CS04NE%2CS0508%2CS0534%2CS0544%2CS0548%2CS05AQ%2CS05DA%2CS0654%2CS06AE%2CS06AF%2CS06AK%2CS0
6C4%2CS06U2%2CS0801%2CS0851%2CS0879%2CS08KA%2CS08TF%2CS09QX%22%2C%22brandCosy%22%3A%22WBBM%22%7D; _pin_unauth=dWlkPU1ETXdNalZpTkRBdE9UQXhZUzAwWWpobUxX
STFaRE10WTJFM01XVm1PVEUxWVdRMg; mbox=session#caf2ce2d3adc47609e4fa1ac588d1a00#1591359906; bmwdtm_hq_sid=k55b3hBo5kgb;
bmwdtm_hq_pcg=topics%7Ctopics%20%3E%20fascination-bmw%7Ctopics%20%3E%20fascination-bmw%20%3E%20efficient-dynamics%7Ctopics%20%3E%20fascination-
bmw%20%3E%20efficient-dynamics%20%3E%20consumption-and-emissions%7Cconsumption-and-emissions; s_lv_s=Less%20than%201%20day; _cs_s=3.1
-
GET: HTTP/1.1 200 OK
Content-Encoding: gzip
Content-Type: text/html; charset=utf-8
Date: Fri, 05 Jun 2020 11:57:59 GMT
Server: Apache
Vary: Accept-Encoding
X-Robots-Tag: noindex
X-UA-Compatible: IE=edge
Content-Length: 9916
Connection: keep-alive
PoC: Source (Email & Web Pages)
Sehr geehrter Herr Dr. B>"[VORNAME|NACHNAME - EXCUTION POINT!],
https://www.bmw.de/de/ssl/requests/rfo-bmw.html#/dlo#%2Fbrand=BM&configI...
https://www.bmw.de/de/ssl/requests/brand-switch-rfi/rfi-type-switch-bmw/...
This is how the malicious code got into the application and can easily be misused for a malicious execution.
So far so good ... lets talk about the reporting. The weak point was reported to the manufacturer BMW on 2020-06-05 via the BMW security program. The content was checked beforehand and the vulnerability was marked as valid. However, the service provider cognitive did not manage to validate it. In the end, no more communication came back from the manufacturer. That's why we checked the vulnerabilities every few months and saw much later when it was completely resolved (nulled/null) to disclose (2021-10-19) without mercy.
Advisory: https://www.vulnerability-lab.com/get_content.php?id=2262



Comments
i find the exploitation of
Add new comment