iPhone 6S & Plus with 3D Touch vulnerable to new Passcode Bypass Vulnerability
iPhone 6S & Plus with 3D Touch (iOS 9.3.1) vulnerable to new Passcode Bypass Vulnerability
Yesterday night around 23:00 o clock a new zeroday vulnerability in the new Apple iOS v9.3.1 with iPhone 6S or Plus models was disclosed to the public. 2016-03-18 the vulnerbaility lab team notified apple with a mailing, that we already detected a new method that evades the controls of the passcode protection mechanism.
In the moment new releases are upcoming the apple mobile developer team is watching for new implemented function that could be exploited to bypass for example the passcode module or icloud protection. In the last updates the apple team announced to integrate the new mechanism that allows to push for the context menu in apps via 3D touch. Ever when we see a new functions, we approve the security controls to the passcode or icloud. In the last years we had successful disclosed several confirmed vulnerabilities, glitches and bugs in the passcode protection mechanism of the ios devices. The method that is get revealed to yesterday allows local attackers with physical device access and default device settings to bypass the passcode lock screen of the iphone 6s and plus.
The 3d touch sensor with the apple display hardware allows to open the basic context menu and new options by low and intensiv push interaction. For example by pushing in the default mail app the messages another context menu for interaction becomes available. The new functions are only available for the apple products like iphone 6S and the iPhone Plus that do support the new hardware.
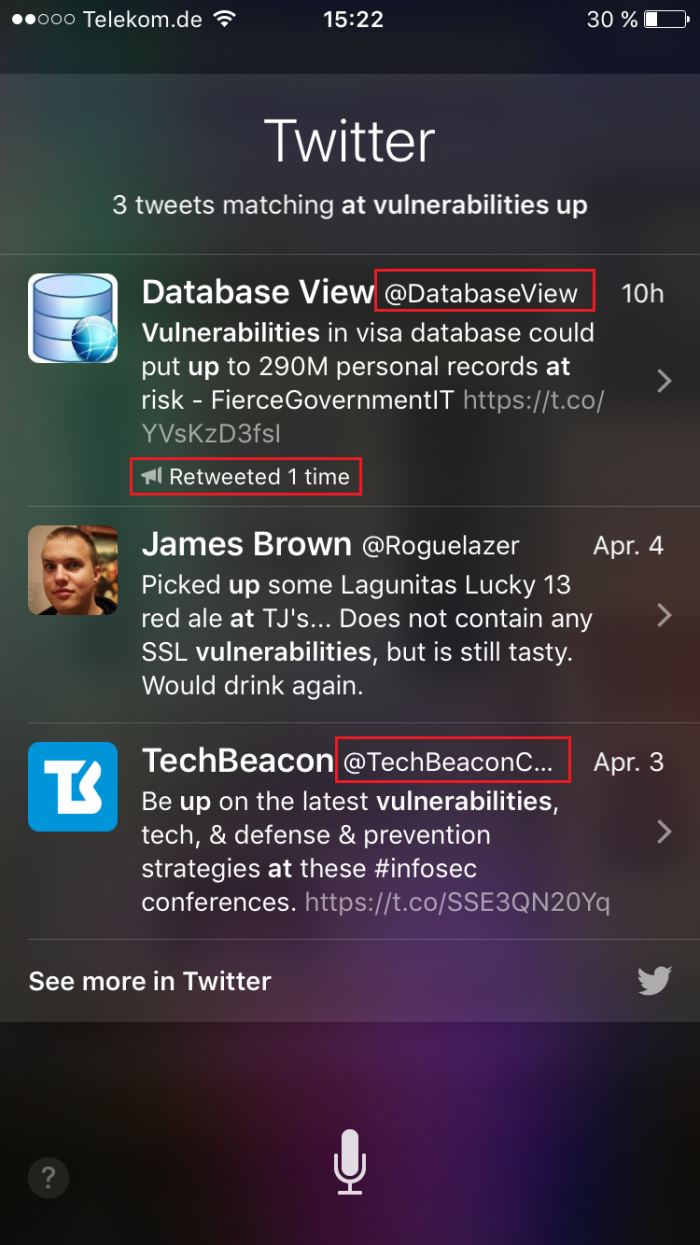
The bug is located in the inner apps @ link format of an installed application. Remote attacker can use siri to request an available runtime app of the task. The interaction is allowed without passcode. After that the attacker surfs over the for example facebook, twitter or yahoo app and search for `@[TAGS]`. The attacker clicks the add tag and holds the button. The new 3d touch sensor of the apple iphone 6s and plus models do allow new interactions by processing to intensiv push the basic context menu becomes visible to the attacker. In the available context menu it is possible to choose to add another new contact. Basically the function is not allowed without passcode auth. Now the attacker push via touch in the new contact the picture / avatar button. Now the screen of the image gallery becomes available as library list. In the next steps the local attacker with physical device access can request the contacts by usage of an email that is connected to an already existing contact in the list. The issue remembers to a bug that was in the early 7.x release of iOS with the calender. In the calender was a yahoo link to the finance stream that allowed us to bypass the display protection of sim locked ios phones.
The security risk of the passcode bypass vulnerability is estimated as high with a cvss (common vulnerability scoring system) count of 6.1. Exploitation of the passcode protection mechanism bypass vulnerability requires a low privileged ios device user account and no user interaction. Physical apple device access is required for successful exploitation. Successful exploitation of the vulnerability results in unauthorized device access, mobile apple device compromise and leak of sensitive device data like the address-book, photos, sms, mms, emails, phone app, mailbox, phone settings or access to other default/installed mobile apps.
Vulnerable Module(s):
[+] PassCode (Protection Mechanism)
Affected Device(s):
[+] iPhone (Models: 6S)
[+] iPhone (Models: 6 Plus)
Affected OS Version(s):
[+] v9.2.1 & v9.3.1
Manual steps to reproduce the vulnerability ...
1. Start the iPhone 6S or iPhone 6 Plus
2. Install for example the default yahoo, twitter or facebook application of the appstore
3. Start the application to the runtime task
4. Set a new passcode via Settings
5. Lock the mobile via power (shutdown) button
6. Open siri by pushing two seconds the home button or use the "hello siri" option
7. Ask siri to search via twitter, yahoo or facebook as slide preview
8. Surf through the feed since a @tag becomes visible or use the search in the preview
9. Push the @tag button - intensive push (6S or Plus)
10. Now the basic context menu becomes visible with new options
11. Choose to add a new contact
12. Open yet the pictures for adding to profile
13. Now, the attacker got already successful access to the photo album of the apple device without secure auth
14. Click to send a message and the mailbox will open without secure auth
14. Successful reproduce of the vulnerability
Solution - Hardening on your own is the Answer!
The vulnerability can be temporarily patched by the end user via hardening of the device settings. Deactivate in the Settings menu the Siri module permanently. Deactivate in the next step the public control panel without passcode. Disallow siri to access picture information or the addressbook by usage of the privacy settings. In the advisory VL ID 1778 (http://www.vulnerability-lab.com/get_content.php?id=1778) we do explain provide another temp fix. As far as this solution is already implemented, the exploitation can't take place against your iOS Plus or 6S touch device.
Note: The version 9.3.1 is still vulnerable after the last update 2016-04-04. The bug was discovered during the analysis of an error issue with the 3D Touch module in the esec labs in germany. The bug was reported by mail to the apple product security team 2016-03-18.
Advisory http://www.vulnerability-lab.com/get_content.php?id=1814
Feel free to review also already original discovered vulnerabilities by the vulnerability laboratory core research team.
http://www.vulnerability-lab.com/get_content.php?id=1778
http://www.vulnerability-lab.com/get_content.php?id=1710
http://www.vulnerability-lab.com/get_content.php?id=875
http://www.vulnerability-lab.com/get_content.php?id=891
http://www.vulnerability-lab.com/get_content.php?id=1092
http://www.vulnerability-lab.com/get_content.php?id=1512
http://www.vulnerability-lab.com/search.php?search=apple&submit=Search
Advisory http://www.vulnerability-lab.com/get_content.php?id=1814
Note: During our reproduce phase, we uploaded the video to youtube with default settings for mistake. The result was that the video became available for 2-3 hours to our abo users. Today around 11:00 we was able to read the results by one of our abo users that downlaoded the video and used it to discover the bug again in the press. So we was forced to finally disclose the issue with all details to today.
Reference(s):
http://www.theregister.co.uk/2016/04/06/security_bods_disclose_lock_bypass_bug_in_ios/
http://www.securityweek.com/iphone-6s-lockscreen-bypass-allows-access-photos-contacts
http://www.zdnet.com/article/iphone-6s-falls-foul-of-new-lock-screen-bypass-flaw/



Comments
ingha
So you dont need a new key cut
Thank you!
Thanks a lot for sharing this great article, I really appreciate the hard work you have put in. Will recommend your site to my friends for sure.
iPhone
jqgfehtix42r@gmail.com
Add new comment