Google Youtube - Persistent Cross Site Vulnerability (Demonstration Video)
Google Youtube - Persistent Cross Site Vulnerability (Demonstration Video)
The independent vulnerability laboratory researcher jasminder pal has discovered a persistent cross site scripting vulnerability in the official google - youtube web-application ui. Google security send a reward of 1337$ to the researcher that discovered the vulnerability during the official bug bounty program. By usage of a filter bypass evasion method the issue became exploitable in different application layers that are connected to the vulnerable values.
Reproduction Steps :
1. Create a playlist name [ t" onmouseover=alert(/xss/); a=" ] . * Without rectangle braces [ ] .
2. Now there are multiple places where this above js code will execute . One is Click edit on any of your uploaded video . On editor page click on Add to Playlist . When you mouseover the playlist name the above js code will execute. Other locations where the code executes is when an youtube user is uploading a video , there it ask for Add to the playlist.
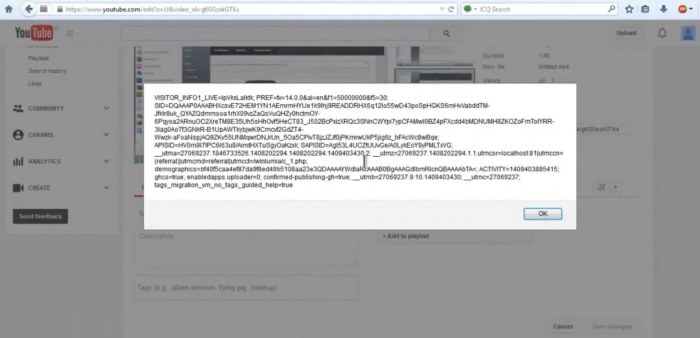
Youtube Queue - Execution of Script Code Payload

Playlist - Execution of Script Code Payload

Google Youtube - Filter Bypass & Persistent Cross Site Scripting Vulnerability (Demonstration Video)
Video: https://www.vulnerability-lab.com/get_content.php?id=1352



Add new comment