Facebook Social Network - Privacy Issue disclosed to Bug Bounty Program by Whitehat
Facebook Social Network - Bug Bounty Program reward 2500$ to Whitehat
A privacy issue has been disclosed by the whitehat "Paulos Yibelo" to the official Facebook Bug Bounty Program. The vulnerability in the framework that was disclosed to the bug report site allows to review restricted context without access permission.
Facebook patched the vulnerability to monday after the report arrived and the researcher disclosed the information 1 day later to the vulnerability laboratory infrastructure.
There is an indirect object reference bug (which they already been notified by someone other than me,) that allows users who convert their accounts to a page using (https://www.facebook.com/pages/create.php?migrate) access everything by requesting mobile based url`s like m.facebook.com/messages/nofications which stores everything their account had and facebook said was removed.
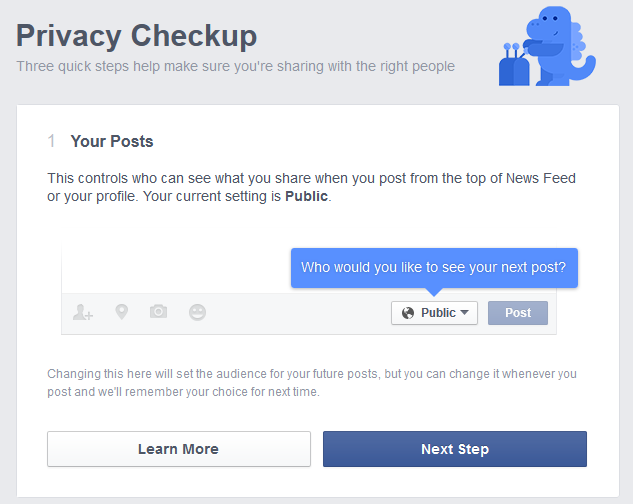
so, using that bug, accessing user`s profile is easy, for example, Himanshu Sharma account converted into a page`s url is https://m.facebook.com/xxx.net (from the mobile interface) simply by requesting his url (since he liked my page), or at least was my friend while I change my account at page - I will be able to see his shares for his privacy setting stating only `Friends`.
The second logic flaw (currently 0day) is, after the first bug fix (privacy?) settings. but now a new flaw seemed to be made, this one however is a little more practically unsafe and you didn`t notice because it only not affects the people who view my profile`s setting but those that are friends with them and arent included with my page.
Request Method(s):
[+] POST
Vulnerable Module(s):
[+] create.php?migrate
Affected Module(s):
[+] Friend Share - Privacy Settings
Proof of Concept Description
Lets say for example I was friends with X before my account was a page, say Y is friends with X but Y isn't my friend.
Now I change my account to a page, which essentially forces X to like my page.
While all this happening, Y have no idea but when Y shares something with the privacy setting "Friends of Friends", I shall be able to see his shares just because X was my friend in the conversion process so Y is my "Friend of Friends".
Time-Line
In case of the vulnerability 2 patches was required to ensure the privacy issue is successful solved. Facebook security team coordinated the disclosure and payed a reward of 2500$ to the independent vulnerability laboratory researcher yibelo.
2014-10-31: Researcher Notification & Coordination (Paulos Yibelo)
2014-11-01: Vendor Notification (Facebook Security Team - Bug Bounty Program)
2014-11-07: Vendor Response/Feedback (Facebook Security Team - Bug Bounty Program)
2014-11-13: Vendor Fix/Patch (Facebook Developer Team - Bug Bounty: 2500$)
2014-11-15: Second Report
2014-12-13: Vendor Fix/Patch (Facebook Developer Team)
2014-12-19: Bug Bounty Payment (Facebook Security Team - Bug Bounty Program)
2014-12-23: Public Disclosure (Vulnerability Laboratory)
Advisory: http://www.vulnerability-lab.com/get_content.php?id=1370



Add new comment